IT Company Blog
Stay Updated
latest tech news with IT Company
Engage & Learn through Tech, IT Support Services, Website Security, Business and many more.










Other Articles
Protecting Remote Teams: 10 Essential Cybersecurity Tips
As Protecting remote teams become a permanent part of many businesses, with the increase of cyber attacks and cyber bullying…
Microsoft Teams – Evolution to Successive Progressive Future
Microsoft Teams Evolves into a Full-Fledged Platform: What You Need to Know from Build Conference Microsoft teams is becoming more…
Remote IT Support for Small Business – Ultimate Guide for Beginners
In today’s tech-driven world, remote IT support for small businesses in Dubai and Abu Dhabi is absolute necessity. Because they…
How to Add URL SEED LIST for Better SEO & Cyber Security Practices
As the digital landscape becomes increasingly competitive, IT companies are leveraging URL seed lists to stay ahead. URL seeds serve…
Auto Block Your Website Against Ping Attacks – Why You Need at Any Cost
Auto Block Website Ping Attacks are a critical measure for any IT company looking to protect its digital assets. Auto…
Strategic IT Infrastructure Services: Streamlining Your Digital Ecosystem
IT Infrastructure services play a critical role in shaping digital ecosystems by providing the technological foundation needed for an IT…
20 Most Powerful and Impulsive Vulnerability Assessment Checklist
With ISO 27001 certification, IT Company lead the way in providing top-notch security solutions. Our vulnerability assessment checklist identifies critical…
Top 10 Vulnerability Assessment Tools to Secure Website
Conducting your first vulnerability assessment tools can seem daunting, but following a structured approach makes it manageable. IT Company provides…
PCI Vulnerability Scans: A Key Component of Risk Management
PCI vulnerability scans are a cornerstone of effective cybersecurity, safeguarding your digital assets and strengthening your security measures. IT…
Linux Vulnerability Management: Leveraging Version 11.4.8 for Optimal Results
Version 11.4.8 is a powerful tool for managing Linux vulnerabilities and operating systems. Even with its advanced capabilities, outdated software…
How To Scan Vulnerabilities on WordPress Using VirtualBox
WordPress sites often face common vulnerabilities. Phishing and cross-site scripting are such examples. Identifying and fixing these security risks are…
Risk Management and Compliance: MSP vulnerability Scanners for Business Protection
MSP vulnerability scanners are essential tools for any IT company aiming to fortify its security posture. As managed service providers…
Cloud Vulnerability Management for Businesses
IT Company cloud vulnerability management plays a crucial role in safeguarding an organization’s digital assets in the ever-evolving landscape of…
Pen Test vs. Vulnerability Scan: Best Practices to Enhance Security Measures for Your Online Business
In today’s digital landscape, online businesses must prioritize security to protect assets, data, and customers. Two vital components are pen…
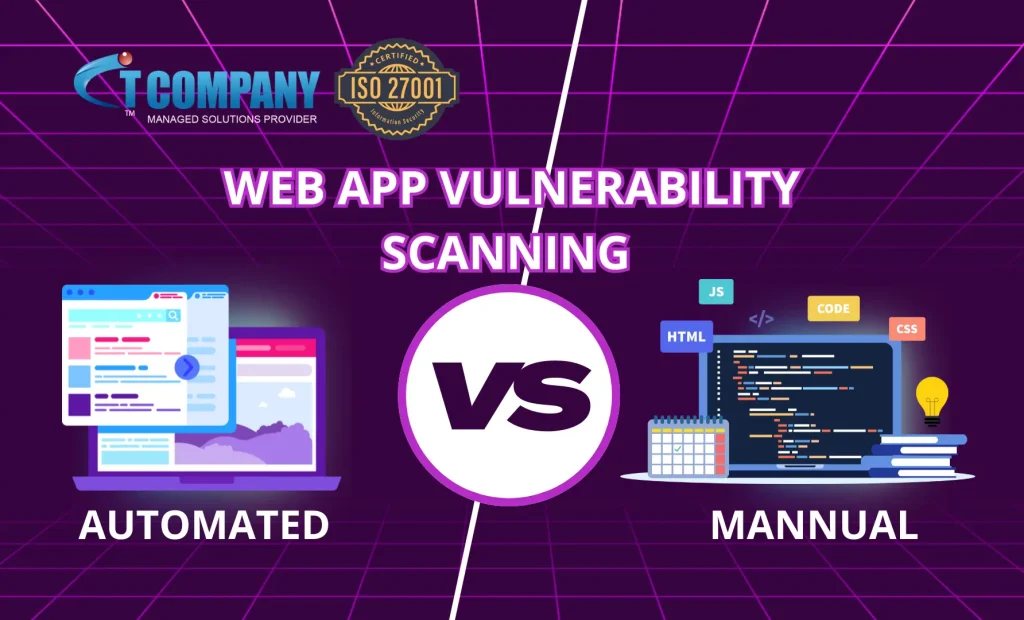
Choosing Between Automated Vs Manual Web App Vulnerability Scanning
In the ever-evolving landscape of web application security, organizations must make critical decisions regarding their vulnerability scanning approach. Choosing between…
WHAT PEOPLE SAY ABOUT US
great service and tech solutions Devil insaanGood
Devil insaanGood Jani SheikhAmazing work done by IT Company. Thankyou for your services.
Jani SheikhAmazing work done by IT Company. Thankyou for your services. Ushna HareemIT Company has made my life so much easier with their superb service and support. Their communication is always refreshing and they've always been up to our expectations when it comes to quality and delivery of the projects. Keep it up 👍
Ushna HareemIT Company has made my life so much easier with their superb service and support. Their communication is always refreshing and they've always been up to our expectations when it comes to quality and delivery of the projects. Keep it up 👍 Usman AzizNever been disappointed with their services. Also they solve most of the technical glitches in blink of an eye. Highly technical team.
Usman AzizNever been disappointed with their services. Also they solve most of the technical glitches in blink of an eye. Highly technical team. Mehrunissa jalilThe team is very dedicated and friendly. Our company is really satisfied from their great expertise.
Mehrunissa jalilThe team is very dedicated and friendly. Our company is really satisfied from their great expertise. bushra shabbirIT Company has design my website and through the process they have been very professional.
bushra shabbirIT Company has design my website and through the process they have been very professional. Sarah BrookeI have hosted my 3 websites with them and they are fast and reliable.
Sarah BrookeI have hosted my 3 websites with them and they are fast and reliable. Ali M
Ali M